Technical Write-ups & Blogs
UltraGroth Protocol Explained
A deep dive into the UltraGroth protocol. We explore how to insignificantly modify the original Groth16 protocol to enable sampling random field elements and conducting lookup checks without sacrificing verification efficiency.
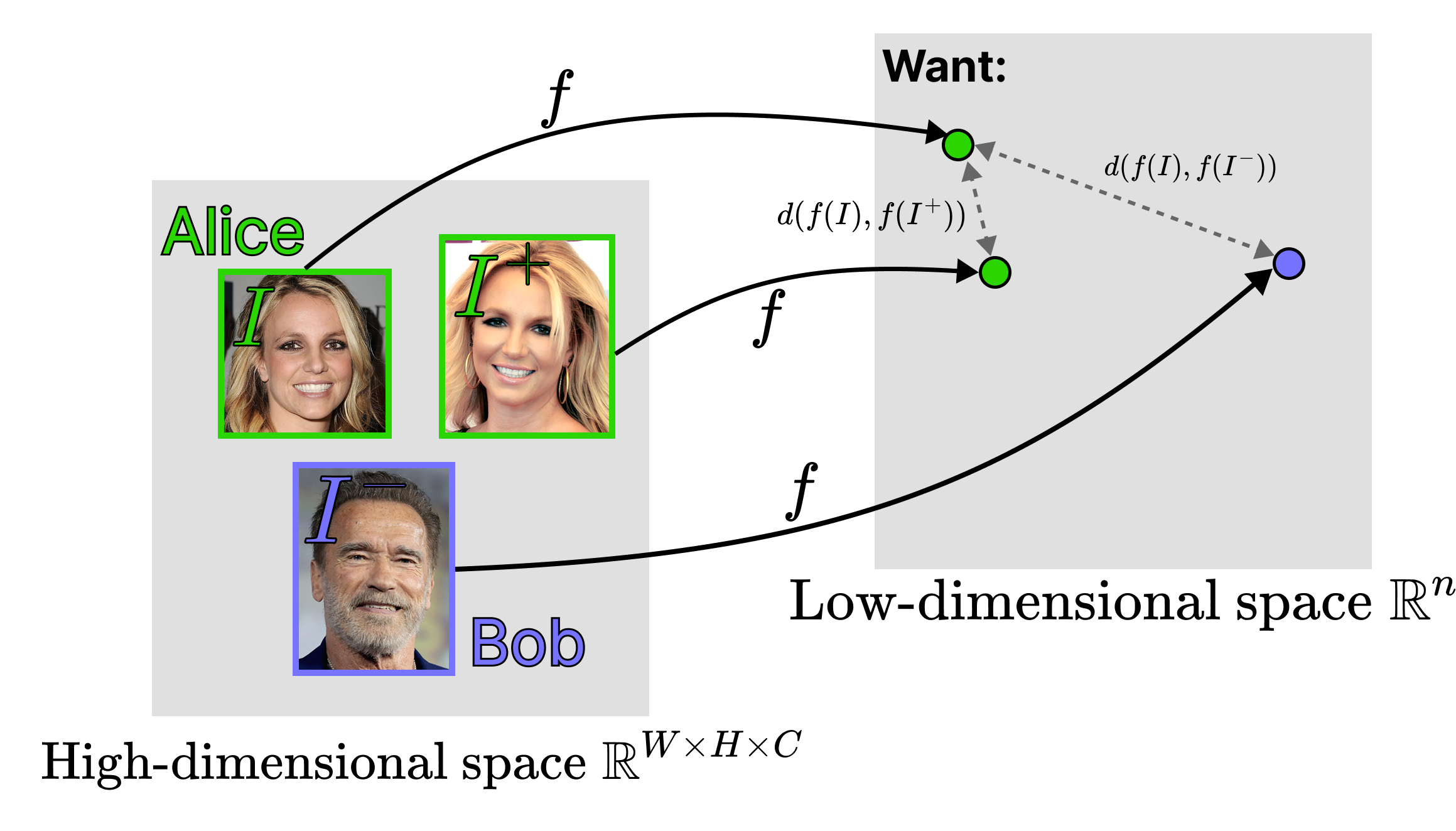
Fuzzy Extractors in a Nutshell
An accessible introduction to Fuzzy Extractors. This blog explains the mathematical mechanics behind reliably deriving strong, uniformly distributed cryptographic keys from noisy, biometric data sources.
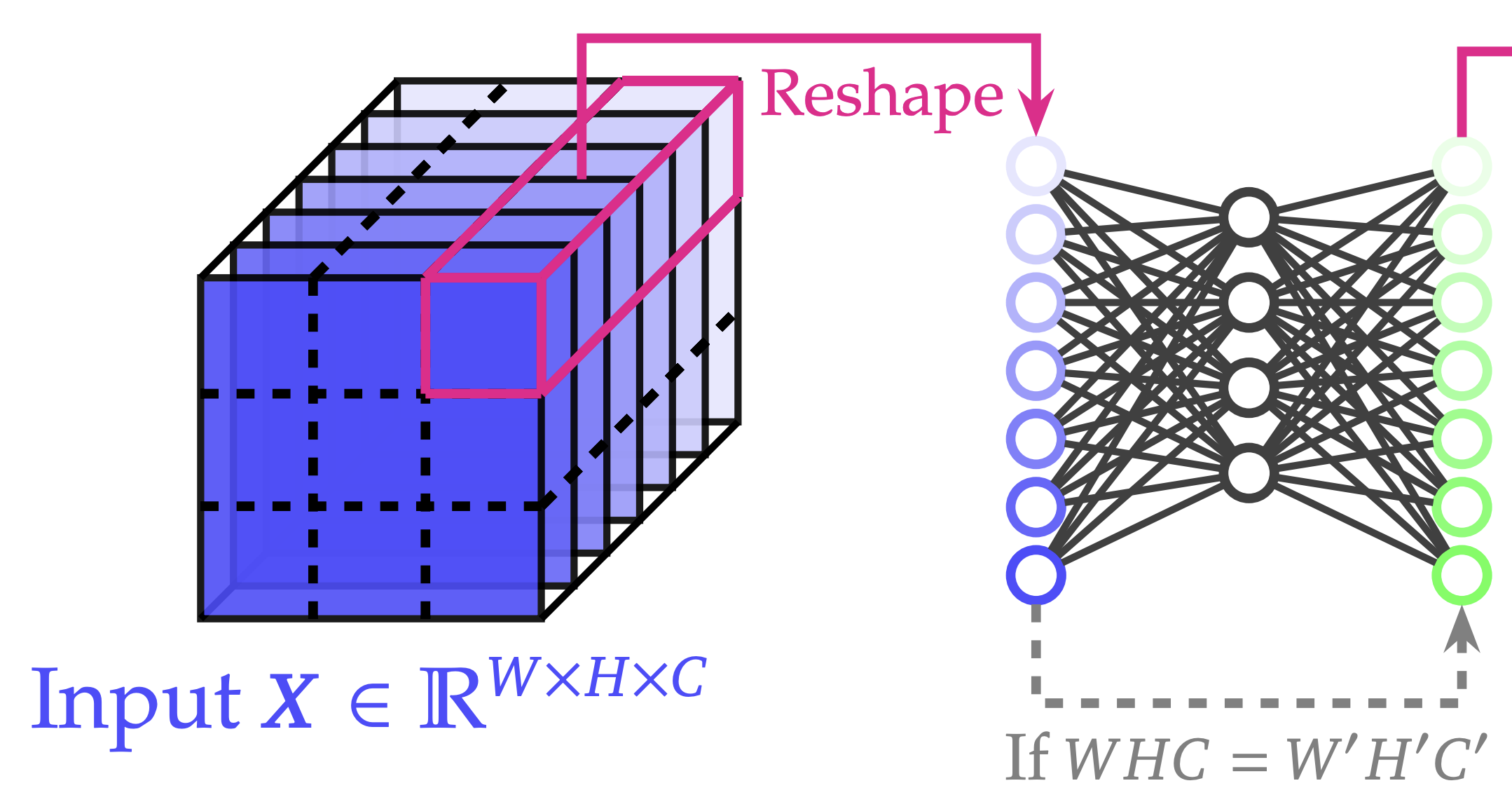
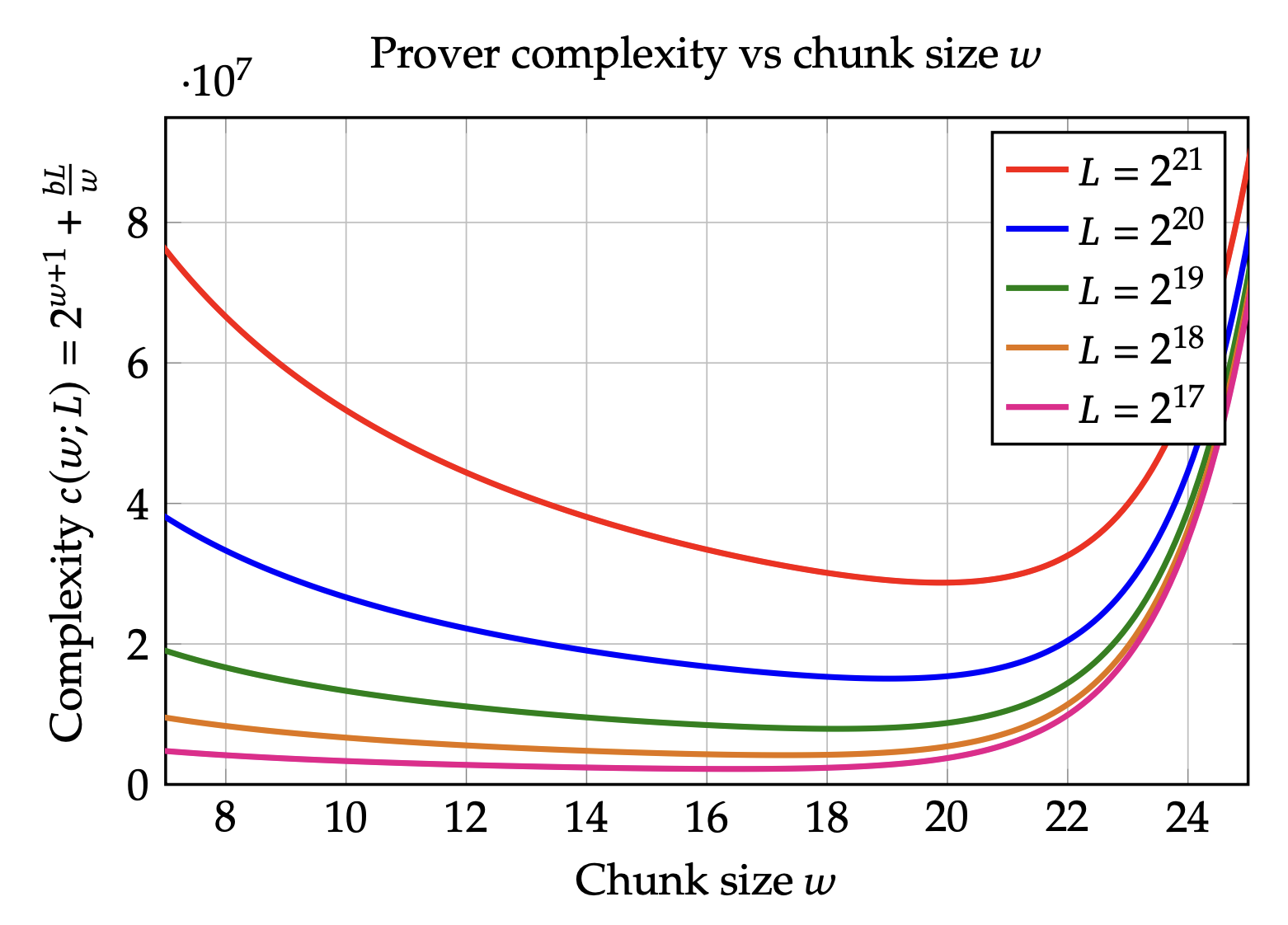
Bionetta: Ultimate Client-Side ZKML. Technical Overview
A technical overview of the Bionetta framework. We demonstrate how to leverage UltraGroth to achieve sublinear constraint complexity for non-linear operations like ReLU in neural networks, paving the way for efficient client-side ZKML.